How to fix HAL_BLOCKED_PROCESSOR_INTERNAL_ERROR BSoD error in Windows 11/10
HAL_BLOCKED_PROCESSOR_INTERNAL_ERROR is a Blue Screen of Death (BSoD) error that occurs in Windows 11/10. HAL stands for Hardware Abstraction Layer, which is a critical component of the Windows operating system responsible for managing communication between the hardware and software. This error typically indicates that the processor has encountered an issue while executing a task, causing the system to crash. It can be triggered by hardware malfunctions, outdated or incompatible drivers, or corrupted system files. Overclocking the CPU or GPU, overheating, or power supply issues can also lead to this error. Additionally, third-party software conflicts or malware infections may contribute to the problem. When this error occurs, the system may restart unexpectedly, leading to potential data loss and disruption. Diagnosing the root cause requires a systematic approach, as it can stem from both hardware and software-related issues. Fortunately, there are several troubleshooting steps available to resolve this error. By addressing the underlying causes, users can restore system stability and prevent future occurrences of the HAL_BLOCKED_PROCESSOR_INTERNAL_ERROR.
How to remove Nitrogen Ransomware and decrypt .NBA files
Nitrogen Ransomware is a malicious software designed to encrypt files on compromised systems, primarily targeting sectors such as construction, financial services, manufacturing, and technology. Upon infection, the ransomware appends the .NBA extension to affected files, effectively rendering them inaccessible without a specific decryption key. For example, a file originally named
document.docx would be altered to document.docx.NBA. This ransomware is notorious for executing advanced anti-analysis techniques, such as detecting virtualization and debugger environments, as well as employing sophisticated code obfuscation. By gathering comprehensive system information, it makes it difficult for victims or analysts to track its operations or reverse the process without the decryption tools held by the threat actors. A ransom note titled readme.txt is typically deposited in affected directories to inform victims of the encryption and the steps needed to initiate communication with the attackers. How to play Lethal Company on Mac
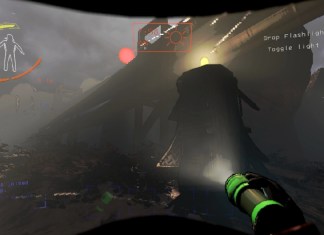
Lethal Company is a dynamic multiplayer horror game that thrusts players into the shoes of a team tasked with exploring eerie locations filled with supernatural threats. The goal is to collect valuable artifacts while avoiding the lurking dangers that haunt each environment. Its gameplay is a thrilling blend of teamwork and strategy, requiring players to communicate effectively to survive and accomplish their objectives. The game’s environments are richly atmospheric, with cleverly designed sound cues and lighting that heighten the tension and keep players on edge. What sets Lethal Company apart is its ability to balance fear with fun, making it appealing to both hardcore horror fans and those new to the genre. Its popularity can be attributed to its engaging co-op experience, which encourages friends to gather and strategize, as well as its unpredictable AI, which ensures that no two sessions are ever the same. Streamers and content creators have also contributed to its success, showcasing the game’s intense and often humorous moments to large audiences. The community around the game is vibrant, with players frequently sharing tips, tricks, and stories from their own terrifying adventures. Though primarily designed for PC, there is interest in seeing if the game can be adapted for Mac users. While there’s no official Mac version yet, some players have found ways to run it through compatibility layers or virtual machines, but this can be hit or miss and might require some technical know-how.
How to play Phasmophobia on Mac
Phasmophobia is a chilling, cooperative horror game that has captivated players with its unique blend of ghost hunting and psychological tension. Players assume the roles of paranormal investigators, working in teams to explore haunted locations, gather evidence, and identify the type of ghost haunting each site. The game leverages an impressive array of equipment, such as EMF readers, spirit boxes, and night vision cameras, to help players interact with and gather clues about the supernatural entities. What sets Phasmophobia apart is its immersive atmosphere, enhanced by realistic audio cues and an eerie ambient soundscape that keeps players on edge. The gameplay is further intensified by the use of voice recognition, allowing players to communicate with the ghosts directly and receive unpredictable responses. Popular due to its engaging cooperative gameplay and the adrenaline rush it delivers, Phasmophobia also benefits from frequent updates that introduce new content and improve the overall experience. The game has become a favorite among streamers and content creators, amplifying its reach and appeal. Despite its popularity, Phasmophobia is primarily designed for Windows, but Mac users can still enjoy the game through workarounds such as Boot Camp or using a Windows virtual machine. While these methods may not provide the same seamless experience as on a native platform, they offer a viable solution for Mac users eager to dive into the haunting world of Phasmophobia.
How to play Squad on Mac
Squad is a tactical first-person shooter that has captivated players with its focus on teamwork and realistic military simulation. Set in large-scale environments, the game emphasizes communication and cooperation among players, requiring them to coordinate strategies and execute plans as cohesive units. With battles featuring up to 100 players, Squad offers an immersive experience where individuals can take on roles such as infantry, medics, or vehicle crew, each contributing to the overall mission success. The game's realistic mechanics, including bullet physics and suppression effects, add layers of complexity that appeal to fans of military simulations. Dynamic weather and day-night cycles further enhance the immersive atmosphere, compelling players to adapt their tactics. One of the reasons for its popularity is the active and dedicated community, which continuously creates and supports mods, adding new content and gameplay variations. Furthermore, Squad's developers regularly update the game, addressing feedback and introducing new features, keeping the experience fresh and engaging. While Squad is primarily available on Windows, running it on Mac requires additional steps, such as using Boot Camp to install Windows or employing virtualization software. This workaround is necessary because there is no native Mac version, but the game's compelling gameplay makes it worth the effort for dedicated fans.
How to play MONSTER HUNTER: WORLD on Mac
MONSTER HUNTER: WORLD is a captivating action role-playing game developed by Capcom that immerses players in a vibrant, living ecosystem where they take on the role of a hunter tasked with tracking and defeating a variety of massive creatures. Set in a beautifully designed open world filled with diverse landscapes, players can explore lush forests, harsh deserts, and treacherous swamps, each teeming with unique wildlife and environmental challenges. The game's core loop revolves around preparing for hunts by gathering resources, crafting weapons and armor, and strategically planning encounters with monsters that have dynamic behaviors and attack patterns. This strategic depth is complemented by a robust multiplayer component, allowing players to team up with friends or strangers online to tackle tougher monsters in cooperative gameplay. One of the reasons for the game's widespread popularity is its ability to appeal to both newcomers and veterans of the series, offering a balanced difficulty curve and a rewarding sense of progression. Furthermore, the game has received critical acclaim for its stunning graphics, intricate world-building, and engaging combat mechanics that encourage experimentation with different weapon types and playstyles. Regular updates and expansions, such as the "Iceborne" expansion, have kept the community engaged with fresh content and challenges. Although MONSTER HUNTER: WORLD was not initially available for Mac, players can potentially run the game on macOS using workarounds such as Boot Camp or third-party software like Wine, though these methods may require technical adjustments and do not guarantee optimal performance. As such, Mac users interested in experiencing this enthralling adventure should weigh the trade-offs before attempting to play on their systems.
How to remove Bbuild Ransomware and decrypt .bbuild files
Bbuild Ransomware is a formidable member of the MedusaLocker family, posing significant threats to users by employing robust encryption techniques to hijack victims' data. Upon activation, it encrypts files and appends a distinctive .bbuild extension, effectively rendering the files unusable without a decryption key. This ransomware uses a combination of RSA and AES encryption methods, which are known for their complexity and security, making unauthorized decryption exceedingly difficult. Victims are typically greeted with a ransom note titled HOW_TO_RECOVER_DATA.html, which is strategically placed in affected directories. This note informs users that their files have been encrypted and urges them to contact the attackers through a Tor-based .onion link or via specified email addresses, threatening dire consequences such as public release or resale of stolen data if the ransom is not paid.
How to remove RdpLocker Ransomware and decrypt .rdplocker files
RdpLocker Ransomware is a malicious software that encrypts the files on an infected computer, leaving them inaccessible until a ransom is paid to the attackers. This ransomware is particularly menacing due to its implementation of sophisticated intermittent encryption, allowing it to rapidly encrypt substantial amounts of user data. Upon infecting a system, RdpLocker appends the .rdplocker extension to encrypted files, transforming them from recognizable formats into something unusable without the correct decryption key. The ransomware also modifies the desktop wallpaper and drops a ransom note labeled as Readme.txt, which details the supposed sophistication of the encryption tool and the steps necessary to recover the compromised files. Victims are instructed to contact the cyber criminals via the email address provided in the ransom note, under the threat of their data being permanently inaccessible or publicly exposed if the ransom payment is not received within 48 hours.