How to remove Trojan:Win32/Pomal!rfn
Trojan:Win32/Pomal!rfn is a sophisticated piece of malware that poses a significant threat to computer systems. This Trojan is known for its ability to disguise itself as legitimate software, making it particularly challenging to detect and remove. Once it infiltrates a system, it can alter critical system settings, manipulate the Windows registry, and even weaken the computer's security defenses. The malware acts as a gateway for additional threats, often downloading and installing other malicious programs without the user's knowledge. Its primary goal is to exploit the infected system, potentially stealing sensitive data or providing unauthorized access to cybercriminals. Users may notice unusual system behavior, including slower performance or unexpected pop-ups, as the Trojan works in the background. Immediate action is required upon detection to prevent further damage and secure the system from ongoing and future threats.
How to remove R2Cheats Ransomware and decrypt _R2Cheats files
R2Cheats Ransomware is a dangerous type of malicious software specifically designed to encrypt victims' files and demand a ransom payment to restore access. When it infects a computer, it appends the _R2Cheats extension to each affected file, rendering it unusable without the appropriate decryption key. For instance, a file named
document.jpg would be altered to document.jpg_R2Cheats. This mechanism effectively locks users out of their own data, exerting psychological pressure to comply with the attacker's demands. The ransomware uses robust encryption algorithms, although details on the specific methods employed remain unclear, ensuring that unauthorized decryption is nearly impossible without the attacker’s tool. Victims are subsequently presented with a ransom note—typically titled ransom_note.txt—which is often found on the desktop or in affected directories. The note demands a payment, in this case, $150 in Roblox gift cards, to be sent via specific communication channels such as an email address or Discord handle. How to remove SHAVELP**SY Ransomware and decrypt .p**sylikeashavel@cyberfear.com files
SHAVELP**SY Ransomware is a malicious program designed to encrypt files on victims' computers, making them inaccessible until a ransom is paid. Discovered through malware samples analyzed via VirusTotal, this ransomware appends the .p**sylikeashavel@cyberfear.com extension to filenames, effectively altering them and signaling their encrypted status. Utilizing sophisticated encryption algorithms, the ransomware ensures that decrypting these files without the proper keys or solutions is nearly impossible. Upon encryption, it generates a ransom note titled README_SHAVEL.txt, informing victims about the situation and demanding payment in exchange for decryption tools. The note often appears on the desktop, urging victims to refrain from renaming files or attempting third-party decryption, claiming this could lead to permanent data loss. In addition to providing contact details for payment arrangements via different communication platforms, the ransom note offers a discounted rate if contact is made within the first 24 hours after encryption. While such tactics aim to persuade victims into paying, experts typically advise against this, as there is no guarantee of recovering files even after complying with payment demands.
How to remove UnicornSpy
UnicornSpy is a sophisticated Trojan malware designed to stealthily infiltrate systems and steal sensitive information. This malicious software primarily targets energy companies, factories, and suppliers of electronic components, making it a significant threat in the industrial sector. It typically spreads through malicious email attachments, often disguised as legitimate files, or via compromised links hosted on unreliable platforms. Once installed, UnicornSpy specifically seeks out smaller files, such as documents and images, which are likely to contain valuable data. Additionally, it targets data stored within the Telegram Desktop directory, aiming to capture private messages and other personal information. This stolen data can be exploited for identity theft, financial fraud, or sold on the dark web. Detecting its presence can be challenging due to its ability to operate silently without noticeable symptoms, necessitating the use of robust antivirus solutions for detection and removal. Regular updates of security software and cautious handling of email attachments are crucial in preventing UnicornSpy infections.
How to remove SteelFox Trojan
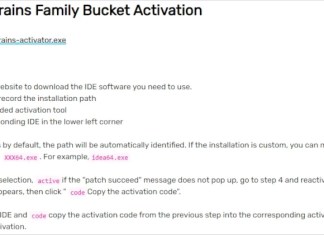
SteelFox Trojan is a sophisticated piece of malware that operates as a bundle with primary components including a data stealer and a cryptocurrency miner. It infiltrates systems under the guise of illegal software activation tools, commonly known as "cracks," deceiving users into installing it themselves. Once inside, the Trojan unleashes its payload by injecting malicious code, escalating privileges, and evading detection by monitoring running processes and avoiding those associated with antivirus software. SteelFox ensures its persistence by auto-starting with each system reboot and exploiting the Microsoft AppInfo service for elevated privileges. Its data-stealing capabilities target sensitive information ranging from system details to user accounts and financial credentials. The cryptominer component, identified as part of the XMRIG malware, exploits system resources to generate cryptocurrency, potentially leading to system overheating and hardware damage. The presence of SteelFox on a device can result in decreased performance, data loss, severe privacy issues, and even financial losses due to identity theft.
How to remove Biobio (Kasper) Ransomware and decrypt .biobio files
Biobio Ransomware is a variant of a known ransomware threat, specifically identified as a mutation of the Kasper Ransomware. It functions primarily by encrypting data on the victim's system, subsequently appending its own specific syntax to the filenames, severely complicating file access without the decryption keys. This ransomware appends the extension .biobio to each compromised file, along with the victim’s unique ID and the attackers' email address, which makes affected data quickly identifiable yet inaccessible. Utilizing robust, modern cryptographic methods, typically an unbreakable encryption algorithm, the malware encrypts files with either symmetric or asymmetric keys, making decryption without the attackers' decryption key practically unfeasible. After encryption is completed, the ransomware generates a ransom note in a text file named biobio ransmoware.txt, which is strategically placed on the victim’s desktop and in other prominent directories. This note details steps for the victim to contact the attackers via email or Telegram for decryption instructions, discouraging the use of third-party decryption attempts.
How to remove MrBeast Ransomware and decrypt .MrBeastOfficial@firemail.cc-MrBeastRansom files
MrBeast Ransomware is a menacing strain of malware designed to encrypt files and demand a ransom from its victims, creating a significant threat to both personal and business data. This ransomware appends the .MrBeastOfficial@firemail.cc-MrBeastRansom extension to the affected files, transforming them into inaccessible fragments that can no longer be opened or utilized until a unique decryption key is obtained. It uses a sophisticated encryption algorithm, often claimed to be unbreakable by its creators, adding an additional layer of complexity to retrieval efforts. Upon infection, it displays a ransom note through a popup and a text file named MrBeastChallenge.txt, instructing victims to purchase a Roblox gamepass and email proof to a specified address for the decryption key. Despite its name, this ransomware bears no connection to the famous YouTuber MrBeast, exploiting his popularity as a deceptive tactic to engage victims.
How to remove Glove Stealer
Glove Stealer is a sophisticated piece of malware known for its capability to harvest sensitive information from compromised systems. Written in .NET, this Trojan targets a wide range of data, primarily focusing on extracting details from web browsers and various software applications. Once it infiltrates a system, it stealthily collects data such as login credentials, cookies, cryptocurrency wallet information, and even two-factor authentication details. The malware is typically spread through deceptive emails that trick users into executing malicious scripts, often without realizing the danger. After gathering enough data, Glove Stealer compresses and encrypts the information into a ZIP file, which is then transmitted to a command-and-control server. Cybercriminals can exploit the stolen information for various malicious purposes, including identity theft, financial fraud, and unauthorized account access. To mitigate the threat of this malware, users are advised to exercise caution with unsolicited emails and to maintain robust security measures on their devices. Regular system scans with reputable antivirus software are crucial in detecting and removing such threats.