How to remove CONTI Ransomware and decrypt .CONTI files
CONTI is a ransomware-type virus that encrypts user's data and keeps it locked until the ransom is paid. Some security experts indicate, that it can be a successor or Ryuk Ransomware. Whilst the encryption is being made, all files including photos, videos, documents, and other regular data will be altered with the new .CONTI extension. This means that the affected files will look like 1.mp4.CONTI or similarly depending on the original name. After this, successful encryption is followed up with a text file (CONTI_README.txt) that is dropped on the desktop of victims. For the moment, it is almost unreal to decrypt your files for free with the help of additional tools. If possible, you can restore your data from backup storage that was created before the infection. Either way, we recommend you to get rid of CONTI Ransomware to prevent further encryptions.
How to remove WastedLocker Ransomware and decrypt .***wasted files
WastedLocker is a file-encrypting malware categorized as ransomware. Programs within this category block access to stored data and require paying a fee to get decryption tools. When ransomware gets settled on your system, all files (videos, images, documents, text files, etc.) will be updated with new extensions. There is a range of extensions used by WastedLocker to highlight encrypted files. Most basic variants include 3 random letters alongside .***wasted extension at the end. For example, files affected by WastedLocker might get a new look of 1.mp4.bbawasted, 1.mp4.rlhwasted or similar. After this, unlike other ransomware that use one common note to explain ransom details, WastedLocker creates separate notes for each infected file. The best thing you can do safe and definite is to get rid of WastedLocker and try to recover data from external backups, if possible. Follow our guide below to find out how.
How to fix 0x8007007e printer error
0x8007007e printer error has been the prime issue touching Windows 10 users since 2019. It prevents people from printing documents and other stuff saying that the printer ran into a problem and cannot finish the job. In fact, this problem represents a big difficulty for many people who got used to printing piles of paper for whatever purpose. There are many reasons that might be the culprit of 0x8007007e error, such as the wrong configuration of printing software, malware, bugged updates, and other options. We have managed to find and test out the most efficient ways to combat this issue and get your printer back to a normal state.
How to fix Windows Update error 0xc1900209
Most Windows problems are usually addressed to update-related topics. Sometimes it may be frustrating to be unable to keep your system always updated due to reasons you are not aware of. 0xc1900209 error was determined to popup because of incompatible software that might have been installed or run into a problem, recently. Besides that, there is a set of generic methods proven to be effective in solving such errors. Before trying to solve the major culprit, we recommend you apply the first 2 methods and do not skip over to next until done. Scroll down to see detailed instructions on how to pull off the resolution for the 0xc1900209 error.
How to remove Fonix Ransomware and decrypt .fonix, .repter or .XINOF files
Also known as FonixCrypter, Fonix Ransomware is an infection, that uses Salsa20 and RSA 4098 algorithms to restrict data accessibility. It encrypts the stored files of various formats - photos, videos, documents, audios, and others that seem to be valuable around regular users. Along the encryption process, the virus assigns compound extensions including e-mail of cybercriminals, personal ID, and .fonix extension at the end. Some versions of Fonix exploit other extensions like .repter and .XINOF. For example, a file like
1.mp4 will be transformed into 1.mp4.EMAIL=[fonix@tuta.io]ID=[1E857D00].Fonix and reset its shortcut as well. It is said that no third-parties tools will be able to decrypt your files because their key is stored on cybercriminal's servers. Instead, developers propose you to buy their decryption key in Bitcoin. If you fail to do this within 2 days, your fee will be doubled immediately. Also, they offer detailed info on how to convert money to BTC in case you have never done it before. As a consolation bonus, extortionists provide decryption of 1 small file for free. Despite this, it is dangerous to pay for the key, because they tend to dumb gullible users, as statistics say. Unfortunately, it is true that there are no feasible methods to unlock files encrypted by Fonix Ransomware. The best way to restore it is by using an external backup of lost files, if possible. How to run Windows programs on Mac
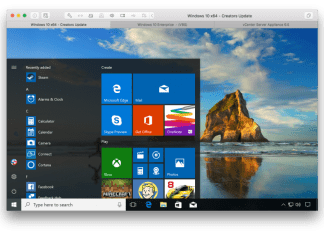
The range of leading operating systems comes down to two major giants - Windows and Mac. Those who get their first experience on Mac after moving from Windows start wondering about how can I use all of the windows-based applications that I used previously. It's been quite a big problem for gaming geeks who strive to spend their break at the helm of iconic games apart from the job without having additional PC nearby. Well, there are various ways that can help you launch these programs even without their actual compatibility on Mac. For this, let's deep dive into our tutorial on how to open Windows programs on Macintosh below.
How to remove HE-HELP Ransomware and decrypt ._HE or ._HE._LP files
HE-HELP Ransomware (Normanzak Ransomware) is a type of malware that encrypts files of users or business holders. Ransomware is considered to be the most dangerous piece since your files get locked forever unless you pay them a certain fee. Unfortunately, because HE-HELP popped in June 2020, security experts have not found a crack to decrypt users’ data for free. Like other infections, the virus assigns new extensions to normal files - either ._HE or ._HE._LP. For instance, 1.mp4 will appear like 1.mp4._HE or similarly after the encryption process is done. Thereafter, the ransomware triggers an automatic opening of a text file called READ_ME_.txt, which is dropped on the victim's desktop. In this note, people can see the encryption report including instructions on how to revive your data. They say that you should contact them via one of the attached e-mails and mention your company name. Cybercriminals also offer a free option to decrypt up to 3 files as a proof sign towards their honesty. Furthermore, they terrify you with threats of publishing your data worldwide. However, if you do not have anything precious to worry about, then you can simply delete it from your computer. In other cases, there is no feasible option to retrieve the affected files with the help of third-parties tools. Either way, we recommend you to wait some time until security experts find a way to handle HE-HELP Ransomware.
How to remove PL Ransomware and decrypt .encoded_PL files
PL is a ransomware infection recently found by cyber experts. The malware of this type encrypts files and demands a fee to get them back. Developers of PL Ransomware simply assign the .encoded_PL, unlike others that use complex combinations of ID numbers with random characters. For instance, a file like 1.mp4 will be changed to 1.mp4.encoded_PL and reset its icon as well. After this, the ransomware script creates a text note (!ALL_YOUR_FILES_ARE_ENCRYPTED) that explains how to decrypt your data. To do so, you should contact them via e-mail to get further instructions for buying a decryption key. It also provides an ability to restore a couple of files for free to prove their integrity. Unfortunately, the research is still underway because security experts have not found a way to decrypt files just yet. However, we can help you with the uninstallation of PL Ransomware to secure further protection in the article below.